Flowtriq Step-by-Step: DDoS Defense for SaaS Builders
Most SaaS founders think their "DDoS strategy" is just a checkbox on their Cloudflare dashboard. They’re wrong. Relying solely on edge-based WAFs is like locking your front door but leaving the windows wide open. When a sophisticated UDP flood or a Mirai-variant attack hits your origin server directly, that "Orange Cloud" won't save your latency.
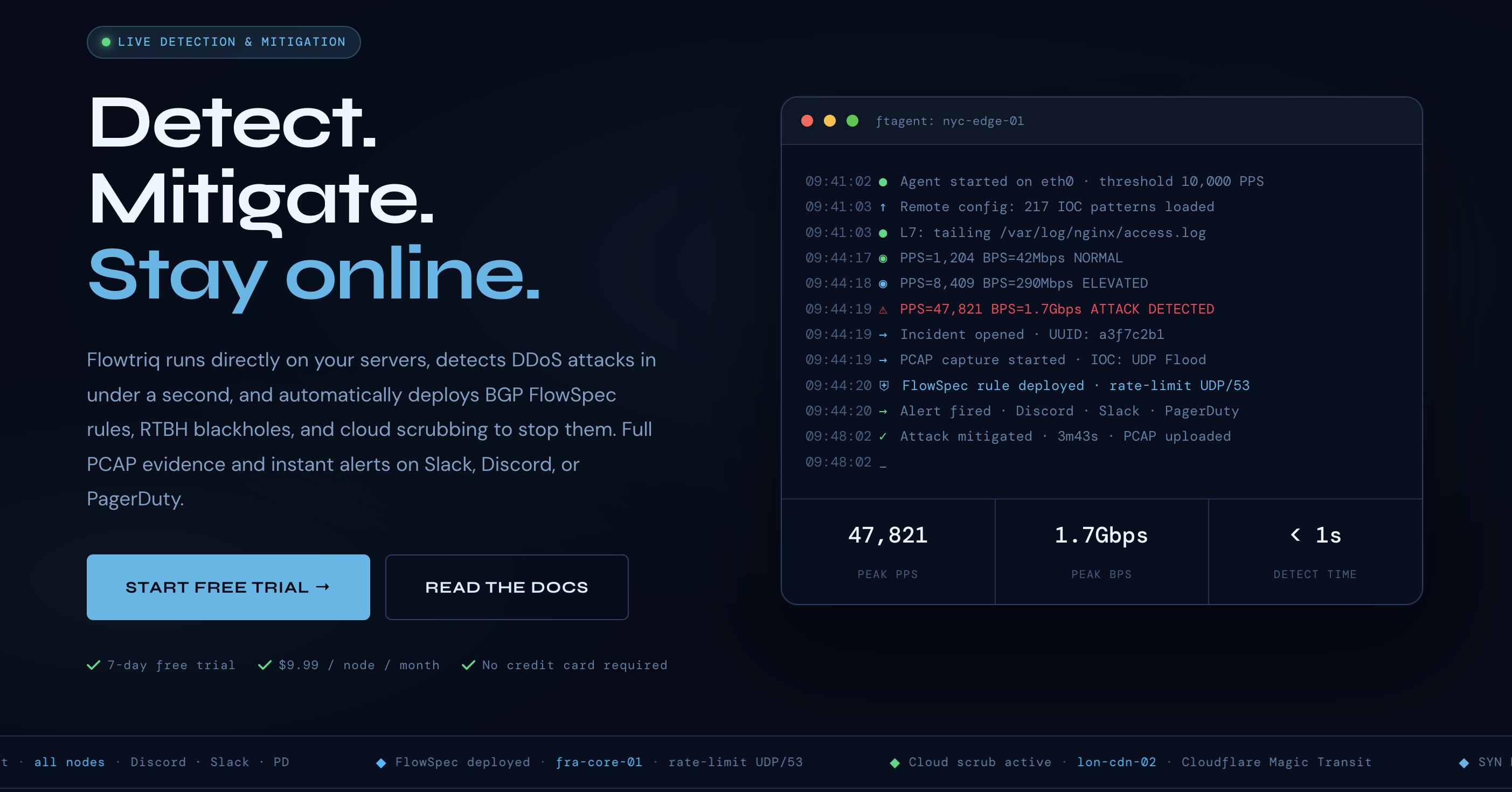
I’ve seen too many "Builders At Scale" hit a wall because they ignored infrastructure-level security until a ransom note landed in their Slack. Scaling isn't just about adding users; it’s about making sure those users can actually reach your API when the internet is on fire. That’s where Flowtriq comes in. It’s not just a filter; it’s a sub-second response system that sits on your Linux nodes and acts before you even get the PagerDuty alert.
The Two-Minute Shield: Deploying Your First Node
Forget the enterprise sales calls and the three-week implementation cycles. If you can copy-paste a line into a terminal, you’re over the hump. After grabbing a 7-day trial at Flowtriq, you’re handed a Python-based agent called ftagent.
The setup is refreshingly "un-corporate." You run the install script on your Linux origin or edge nodes, and it hooks directly into the Network Interface Card (NIC). It doesn’t just look at logs; it reads packets. Within about 120 seconds, your node is talking to the Flowtriq dashboard. The best part? It starts learning your "normal" immediately. You don't have to guess if 5,000 PPS (packets per second) is a marketing spike or a SYN flood; the system figures that out for you.
Beyond the Dashboard: Features That Actually Matter
When you’re moving from builder to leader, you stop playing with toys and start using tools that automate your anxiety. Here are the three features I actually use:
- ▸Sub-Second Auto-Mitigation: Most tools "detect" an attack in 30 seconds and "mitigate" in three minutes. By then, your DB connections are Maxed and your site is down. Flowtriq hits back in under one second by deploying BGP FlowSpec rules or RTBH (Remote Triggered Black Hole) filtering.
- ▸The Forensic "Time Machine": Every time an attack is detected, Flowtriq triggers a full PCAP (Packet Capture). If you’ve ever tried to explain a downtime event to a Tier-1 VC or a major enterprise client, having the raw packet data to show exactly what happened is your "get out of jail free" card.
- ▸Dynamic Runbooks: You can chain actions. For example: "If attack > 1Gbps, trigger Cloudflare Magic Transit AND alert the #ops-war-room on Slack." It’s basically Zapier for network warfare.
Pro Tips: Scaling Your Defense Without the Overhead
In my experience, the biggest mistake SaaS teams make is treating every server like an island. If you’re running a distributed cluster, use Flowtriq’s Multi-Node Management.
My "hot take" for SaaS pros: Don't just monitor your web servers. Monitor your database's public-facing sync points and your staging environments. Attackers love hitting the "soft" infrastructure that isn't behind your main CDN. At $9.99 a node, there is zero excuse to leave your back-end services exposed. Also, keep an eye on their Threat Intel feed; Flowtriq’s team literally discovered the Mirai botnet kill switch (CVE-2024-45163), so their IOC (Indicator of Compromise) library is usually miles ahead of the generic lists.
Common Pitfalls (And How to Stay Upright)
- ▸Ignoring the "Learning" Phase: Don't trigger a massive load test five minutes after installing the agent. Give the dynamic baseline a few hours to understand your traffic patterns, or you’ll end up blackholing your own stress test.
- ▸Over-complicating Alerts: Just because you can alert via SMS, Slack, and PagerDuty doesn't mean you should. Use the sub-second Slack alerts for awareness, but save the SMS for when the auto-mitigation fails to clear the threat.
- ▸Forgetting the "Human" Element: Flowtriq provides status pages. Use them. When an attack happens, your users care more about communication than the technical details of a UDP flood.
How It Compares to the Ecosystem
While Flowtriq is my go-to for infrastructure-level protection, you need to know where it fits in your stack:
- ▸For Global Edge Protection: If you need a massive global network to absorb Terabit-scale attacks before they even reach your ISP, you're likely looking at Cloudflare. Flowtriq is what you use to protect the servers behind the edge.
- ▸For Application-Level Monitoring: If your problem isn't DDoS but rather slow database queries, check out Datadog for full-stack observability.
- ▸For Team Coordination: When Flowtriq fires an alert, you need a place to manage the incident. PagerDuty remains the gold standard for getting the right engineer on the phone.
Conclusion: Is Flowtriq Right for You?
If you are a solo dev running a hobby project on a $5 DigitalOcean droplet, you might not need this yet. But the moment "building becomes scaling"—when downtime starts costing you $100s or $1,000s per hour in churn and reputation—Flowtriq is a no-brainer.
It’s lightweight, it’s built by people who actually contribute to the security community, and it costs less than two fancy lattes per month. Don't wait for your first ransom note to start thinking about packet-level security. Install the agent, set your runbooks, and get back to building.